- 23 Apr 2025
- 3 Minutes to read
- Print
- DarkLight
Microsoft 365
- Updated on 23 Apr 2025
- 3 Minutes to read
- Print
- DarkLight
Microsoft 365, formerly Office 365, is a product family of productivity software, collaboration and cloud-based services owned by Microsoft. This adapter allows you to ingest audit events from the Office 365 Management Activity API.
Microsoft 365 events can be ingested in LimaCharlie and observed as the office365 platform.
Adapter Deployment
Microsoft 365 events are ingested via a cloud-to-cloud Adapter configured specifically to review M365 events. When creating an Adapter, the following data points are required:
domain: Office 365 domaintenant_id: Office 365 tenant IDpublisher_id: Office 365 publisher ID ( in the case of single-tenant Apps, the PublisherID is the same as the Tenant ID)client_id: Office 365 client IDclient_secret: Office 365 client secretendpoint: Office 365 API endpointcontent_types: content types of events to ingest- Options include:
Audit.AzureActiveDirectoryAudit.ExchangeAudit.SharePointAudit.GeneralDLP.All
- Default is all of the above
- Options include:
If creating a Microsoft 365 Adapter via the Web UI, the helper form will navigate you through providing these values.
Establishing a cloud-to-cloud connector between LimaCharlie and Office 365 requires a few steps to provide the correct permissions for the Office 365 Management Activity API.
Configuring a Microsoft 365 Adapter in the Web UI
Preparing Office 365 details
To establish an Office 365 adapter, we will need to complete a few steps within the Azure portal. Ensure that you have the correct permissions to set up a new App registration.
Within the Microsoft Azure portal, create a new App registration. You can follow Microsoft's Quickstart guide here.
The LimaCharlie connector requires a secret for Office 365 data. You can create one under
Certificates & secrets. Be sure to copy this value and save it somewhere - you can only view it once.

- Additionally, you'll need to ensure that the app has the correct permissions to view Office 365 data via the Management API. Within
API Permissions, configure the following permissions:ActivityFeed.Read(Delegated & Application)ActivityFeed.ReadDlp(Delegated & Application) [if you want DLP permissions]
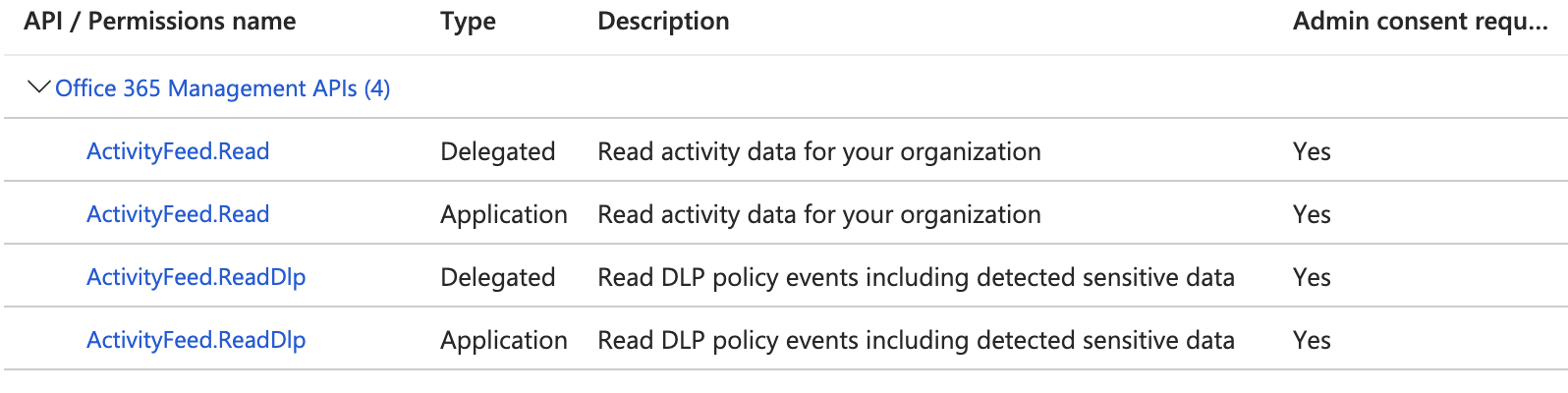
Additionally, you may need to grant admin consent to the above permissions.
At this point, you should have all the details you need to configure the Adapter.
Setting Up the Adapter
Within the LimaCharlie web application, select + Add Sensor, and then select Office 365:
You can select a pre-existing installation key or create a new one, unique for this adapter. Once an Installation Key is selected, you will be prompted with a form to finish setting up the adapter. Choose your desired adapter name, and provide the following values:
| Item | Azure Portal Location |
|---|---|
| Domain | Home |
| Tenant ID | App Registration Overview |
| Publisher ID | App Registration Overview |
| Client ID | App Registration Overview |
| Client Secret | Created during creation in Certificates & secrets |
| API Endpoint | enterprise, gcc-gov, gcc-high-gov, or dod-gov |
Finally, you will also need to select a "Content Type" to import. This is the type of events you want to bring in to LimaCharlie. The options are as follows:
Audit.AzureActiveDirectoryAudit.ExchangeAudit.SharePointAudit.GeneralDLP.All
Without a value, the default is all of the above.
Click Complete Cloud Installation, and LimaCharlie will attempt to connect to the Microsoft Office 365 Management API and pull events.
Sample D&R Rule
When ingested into LimaCharlie, Office 365 data can be referenced directly in your D&R rules. You could do this via a platform operator:
op: is platform
name: office365
We can also reference Office 365 events directly. The following sample rule looks at FileAccessed events from anonymous user names, and reports accordingly.
# Detection
event: FileAccessed
path: event/UserId
op: contains
value: anon
# Response
- action: report
name: OneDrive File Accessed by Anonymous User
Note that in the detection above, we pivot on the FileAccessed event, which is associated with SharePoint activity. Available event types will depend on source activity and events ingested. More information on audit log activities can be found here.

